- The Accused and Law Enforcement
- DNA Forensics and Law Enforcement
- Law Enforcement and Information Technology
- Law Enforcement and Terrorism
- Law Enforcement and Crime Investigations
- Guides to Cooperating with Law Enforcement
- Military Law Enforcement and Military Police
- Law Enforcement and Medical Records
- Miscellaneous Library Materials Relating to Law Enforcement
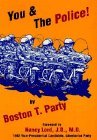
The Accused and Law Enforcement
The Police Contact: Silence is Golden
There are literally thousands of people behind bars today who tried to talk their way out of a law enforcement contact. Don’t fall for the ploy. Law enforcement officers are trained to bluff you into making denials or statements. They will appear friendly and reasonable. They will appear willing to help resolve the matter. They will tempt you to talk about it and appear sympathetic. Don’t fall for it. Say nothing. Give them nothing. Deny nothing. Give them nothing. Stick your tongue between your teeth and bite down - HARD. You are to be a marble statue. You do not exist. You have no past, you have no address, you have no name, you have no social security number. You are to give them nothing whatsoever to work with.
What You Should Know If You’re Accused of a Crime
Anyone confronting the bewildering and, to many, the intimidating and nerve shattering complexities of the New York State criminal justice system for the first time in his or her life, will find Joyce David’s handbook outlining the ABC’s of the system an invaluable tool in dealing with them.
If an Agent Knocks
Federal Investigators and Your Rights
What To Do If The Police Come To Confiscate Your Militia Weapons
The Fourth Amendment protects you against unreasonable searches and seizures. If the police want to search your house without your consent, they need a warrant. Warrants may only be issued upon a showing of probable cause, supported by an affidavit. The facts contained in the affidavit must do more than support a mere suspicion. The test is whether the information in the affidavit would justify a person of prudence and caution in believing that an offense is being committed, e.g. that prohibited weapons can be found on your premises. The requirement of probable cause for the issuance of warrants is one of your most precious constitutional protections. The Fifth Amendment protects you against giving evidence against yourself, i.e., your right to remain silent. Just as you cannot be compelled to testify against yourself in a criminal trial, neither can you be compelled to answer a policeman’s questions about that AR-15 you bought a couple of years ago and never surrendered. Don’t be bashful about invoking this right. It’s always better to remain silent and appear guilty than to open your mouth and prove it.
ACLU pocket card on police encounters
Police abuse is a serious national problem — and one that especially affects young people and people of color. While many police officers do strive to be courteous, and while we all understand the stress and danger involved in policing, each of us has the right to be treated with respect — and without abuse — by the police. To fight police abuse effectively you need to know your rights. There are some things you should do, some things you must do and some things you cannot do. If you are in the middle of a police encounter, you need a handy and quick reference to remind you what your rights and obligations are. That’s why the ACLU is making this pocket card available as a downloadable file. You can photocopy this and carry it in your wallet, pocket or glove compartment to give you quick access to your rights and obligations concerning police encounters.
The Law and You: Guidelines for interacting with law enforcement officials
Guidelines for Interacting with Law Enforcement Officials — for black people. Very odd NAACP document.
DNA Forensics and Law Enforcement
What Every Law Enforcement Officer Should Know About DNA Evidence
Just as today’s law enforcement officer has learned to look routinely for fingerprints to identify the perpetrator of a crime, that same officer needs to think routinely about evidence that may contain DNA. Recent advancements in DNA technology are enabling law enforcement officers to solve cases previously thought to be unsolvable. Today, investigators with a fundamental knowledge of how to identify, preserve, and collect DNA evidence properly can solve cases in ways previously seen only on television. Evidence invisible to the naked eye can be the key to solving a residential burglary, sexual assault, or child’s murder. It also can be the evidence that links different crime scenes to each other in a small town, within a single State, or even across the Nation. The saliva on the stamp of a stalker’s threatening letter or the skin cells shed on a ligature of a strangled victim can be compared with a suspect’s blood or saliva sample. Similarly, DNA collected from the perspiration on a baseball cap discarded by a rapist at one crime scene can be compared with DNA in the saliva swabbed from the bite mark on a different rape victim.
DNA Evidence: What Law Enforcement Officers Should Know
Proper use of DNA (deoxyribonucleic acid) evidence at trial can help to seal a conviction or obtain an acquittal. It is therefore very important that police officers know how to manage crime scenes in order to make sure DNA evidence is collected properly. If such evidence is to be useful in court, law enforcement personnel should employ specific procedures to protect and preserve this sensitive biological material.
PCR Based DNA Profiling: Law Enforcement in the Laboratory
Since the late 1980s, DNA profiling - a technique that can identify an individual to a certainty of one in a million - has proven to be a powerful investigative tool for law enforcement. Violent crime and sexual abuse cases that once might have gone unresolved due to insufficient evidence are now being solved on the testimony of blood stains, hair, or semen left at the scene of a crime.
Law Enforcement and Information Technology
The Law Enforcement and Forensic Examiner Introduction to Linux A Beginners Guide
This purpose of this document is to provide an introduction to the GNU/Linux (Linux) operating system as a forensic tool for computer crime investigators. There are better books written on the subject of Linux (by better qualified professionals), but my hope here is to provide a single document that allows a user to sit at the shell prompt (command prompt) for the first time and not be overwhelmed by a 700-page book.
Maintaining Forensic Evidence for Law Enforcement Agencies from a Federation of Decoy Networks: An Extended Abstract
Network forensics involves the preservation, identification, extraction, documentation, and interpretation of network data. It lies at the intersection of electronic information systems and the law, and involves reviewing a compromised system and piecing together step-by-step what happened. Law enforcement agencies may be called upon to investigate intrusions if an intruder gains unauthorized access to a computer system protected by law. They require comprehensive and credible network forensic evidence of the potential cyber crimes to prosecute the intruders or to seek legal warrants to monitor suspected activities.
The Use of Computerized Crime Mapping by Law Enforcement: Survey Results
Computerized crime mapping technology enables law enforcement agencies to analyze and correlate data sources to create a detailed snapshot of crime incidents and related factors within a community or other geographical area. Interest in this technology within the law enforcement community appears to be gaining momentum, but until recently no systematic data existed on how widely it is used. As a first step in understanding law enforcement agencies’ knowledge of crime mapping, the Crime Mapping Research Center (CMRC) of the National Institute of Justice (NIJ) conducted the nationwide Crime Mapping Survey over 15 months to determine who uses geographical information systems (GIS) and why other agencies are not using this mapping technology.
Encryption and Law Enforcement
Developments in encryption technology, products and services carry significant benefits in increasing consumers’ levels of trust in the Internet, and particularly in e-commerce. However, they also give rise to a number of challenges for law enforcement, where it will become more difficult to derive intelligence from lawfully intercepted communications and retrieved data. This report considers the Government’s response to the issues of encryption, e-commerce and law enforcement.
Intrusion Detection, Internet Law Enforcement and Insurance Coverage to Accelerate the Proliferation of Internet Business
In this article, we propose a framework to accelerate the ubiquitous capitalization of Internet as a vehicle to merchandise goods and services. The motivation for proposing this framework derives from the fact that many consumers and small-to-medium-sized companies are still hesitant to use Internet to shop, trade and disclose sensitive information such as credit card numbers. While IT security technologies and products are widely available, there are still gaps that have to be filled in before Internet becomes a truly viable and profitable channel to do business.
Electronic Crime Scene Investigation: A Guide for Law Enforcement
The Internet, computer networks, and automated data systems present an enormous new opportunity for committing criminal activity. Computers and other electronic devices are being used increasingly to commit, enable, or support crimes perpetrated against persons, organizations, or property. Whether the crime involves attacks against computer systems, the information they contain, or more traditional crimes such as murder, money laundering, trafficking, or fraud, electronic evidence increasingly is involved. It is no surprise that law enforcement and criminal justice officials are being overwhelmed by the volume of investigations and prosecutions that involve electronic evidence. The series of guides will address the investigation process from the crime scene first responder, to the laboratory, to the courtroom.
The Internet and Law Enforcement Surveillance: Law Enforcement Concerns Can Be Addressed Without Regulation, Which Would Stifle Innovation, Raise Costs, Risk Security
There is nothing untappable about packet or Internet technology. Packet services currently available for voice and data are tappable at one or more points in the networks, and service providers are quite willing to work with law enforcement to satisfy interception orders quickly and fully. But the Internet is different from the traditional telephone network, and government agencies should not expect that surveillance will be carried out on the Internet the same way it is carried out in the circuit-switched telephone network. The digital revolution has produced many means of communication and it is not reasonable to require that all of them identify communications and route traffic the same way that the telephone network does.
Simple Law Enforcement Monitoring
Presentation by Cisco to the IETF on Law Enforcement Monitoring of the Internet
Law Enforcement Records Management Systems A Public Safety Primer
A law enforcement agency needs a Records Management System (RMS) to enter information regarding criminal events that occur in their jurisdiction.
A Guide for Applying Information Technology in Law Enforcement
The information revolution of the past two decades has resulted in more people having faster access to more accurate data than ever before. Both the public and law enforcement practitioners expect agency information systems to respond quickly with an enhanced ability to recognize crime patterns and problem areas. As a result, law enforcement agencies need to improve their information systems to better analyze and use the data they collect. This guide is intended to help law enforcement practitioners plan and implement information system upgrades and address connectivity and data sharing issues. It is intended to be a primer rather than a definitive treatise on the subject. The authors’ goal is to help public safety agencies integrate such public safety information systems as computer-aided dispatch, records management, geographical information systems, and mobile computing. Using the principles outlined in this guide, law enforcement professionals can choose the technologies that best suit their needs and incorporate them into their day-to-day operations.
Law Enforcement and Terrorism
Strengthening Law Enforcement Capabilities to Combat Terrorism
Law enforcement as a counter-terrorism tool faces two major challenges: technological change and globalization. These affect national law enforcement across the board. Making law enforcement more effective in meeting these challenges requires taking advantage of new technologies, with adequate legal safeguards for civil liberties; and using globalization as a positive force to build better international law enforcement, through greater information sharing, coordination and cooperation. For the United States, a crucial part of responding to these two challenges will also be to reconsider the constraints placed on law enforcement and intelligence agencies as a result of the political turmoil of the 1970s.
Report On Financial Privacy, Law Enforcement And Terrorism
Prior to the September 11 attacks on the United States, information exchange and money laundering were topics of increasing concern and focus. The primary government initiatives, however, were in the tax administration arena. These initiatives included the OECD harmful tax competition initiative, the proposed United Nations International Tax Organization, the proposed IRS interest reporting regulations, the IRS qualified intermediary (QI) rules and the effective incorporation of “know your customer” (KYC) banking regulations into the U.S. QI rules. After the attacks, there was a renewed interest in money laundering statutes and regulations as a means of aiding government in its antiterrorism efforts. This was demonstrated, most notably, by the enactment in late October of the International Money Laundering Abatement and Financial Anti-Terrorism Act of 2001.1 Although there has been a flurry of administrative and legislative activity, it has become clear from Congressional testimony and reports in the U.S. and European news media that the current international information sharing framework is simply inadequate and misdirected for purposes of addressing the threat that terrorism poses to the United States and allied countries. Priorities should be refocused in light of the heightened terrorist threat and the mechanisms that will aid the effort to combat global terrorism should be reviewed.
Inventory of State and Local Law Enforcement Technology Needs to Combat Terrorism
Recent acts of terrorism within the United States, such as the bombings of the World Trade Center in New York City and Centennial Olympic Park in Atlanta, have focused attention on the ability of law enforcement to manage these incidents and investigate individuals and groups suspected of planning or executing terrorist acts. Of particular concern is the gap between technologies available to and used by law enforcement - especially State and local agencies - and the advanced technologies used by persons and groups planning terrorist acts.
Intelligence and Law Enforcement: Countering Transnational Threats to the U.S.
In the post-Cold War world, terrorism, narcotics trafficking, and related money laundering are perceived both as criminal matters and as threats to the nation’s security. Often collectively termed transnational threats, these issues have become the concerns of law enforcement agencies as well as the U.S. Intelligence Community. Two foreign banking scandals in the late 1980s led to efforts to ensure that information in the possession of intelligence agencies would, in the future, be made available to law enforcement officials. In the mid-1990s, the Federal Bureau of Investigation began assigning additional agents to newly created offices worldwide. The tragic events of September 11, 2001 provide a clear demonstration of how large a threat international terrorism can become to national security. The Bush Administration and Congress have moved rapidly to promote intelligence/enforcement cooperation among U.S. agencies in the campaign against Al Qaeda. This report looks at the separate roles and missions and distinct identities of intelligence and law enforcement agencies. Coordinating their efforts has raised significant legal and administrative difficulties that have been only partially overcome despite the creation of elaborate coordinative mechanisms under the oversight of the National Security Council. Some observers also have expressed concerns about the greater use of information derived from intelligence sources in judicial proceedings, fearing that it may lead to over-reliance on surreptitious means of information collection and, thus, undermine civil liberties. Other observers have cautioned that redirecting intelligence assets to collect information for legal cases may reduce support available to military commanders and policymakers. Some others believe that there may also be an overemphasis on law enforcement in dealing with problems arising abroad. The report notes the employment of covert actions by intelligence agencies in certain law enforcement efforts.
Assessing Florida’s Anti-Terrorism Capabilities
The events of September 11, 2001 weakened the American public’s confidence in the government’s ability to protect our homeland from terrorist attack. While international terrorism is principally a Federal responsibility, in light of new realities, states must do more to prepare to combat all types of terrorism. Florida’s economic prosperity depends heavily on travel and tourism, and it’s citizens and visitors have the right to feel and be safe. It is important that Florida’s government leaders take immediate steps to ensure that this State is safe from and prepared to respond in the event of a terrorist attack.
Law Enforcement and Crime Investigations
Eyewitness Evidence A Guide for Law Enforcement
Eyewitnesses frequently play a vital role in uncovering the truth about a crime. The evidence they provide can be critical in identifying, charging, and ultimately convicting suspected criminals. That is why it is absolutely essential that eyewitness evidence be accurate and reliable. One way of ensuring we, as investigators, obtain the most accurate and reliable evidence from eyewitnesses is to follow sound protocols in our investigations.
Eyewitness Evidence: A Trainer’s Manual for Law Enforcement
Eyewitnesses play a critical role in our criminal justice system. They are often essential to identifying, charging, and ultimately convicting perpetrators of crime and in some cases may provide the sole piece of evidence against those individuals. For these reasons, the value of accurate and reliable eyewitness evidence cannot be overstated.
Crime Scene Investigation: A Guide for Law Enforcement
Actions taken at the outset of an investigation at a crime scene can play a pivotal role in the resolution of a case. Careful, thorough investigation is key to ensure that potential physical evidence is not tainted or destroyed or potential witnesses overlooked.
Law Enforcement: Information on Timeliness of Criminal Fingerprint Submissions to the FBI
By positively confirming identifications and linking relevant records of arrests and prosecutions, fingerprint analysis provides a basis for making fundamental criminal justice decisions regarding detention, charging, bail, and sentencing. In 1999, the FBI implemented the Integrated Automated Fingerprint Identification System (IAFIS) - a computerized system for storing, comparing, and exchanging fingerprint data in a digital format. The FBI’s goal under IAFIS is to ultimately achieve paperless processing and to provide a response within 2 hours to users who submit criminal fingerprints electronically. Maximizing the benefits of rapid responses under IAFIS depends largely on how quickly criminal fingerprints are submitted by local and state law enforcement agencies. Concerns have been raised that, after arrests are made by some local or state law enforcement agencies, periods of up to 6 months may elapse before the criminal fingerprints are submitted for entry into IAFIS. GAO examined (1) the importance of IAFIS processing to local and state law enforcement agencies, (2) the progress these agencies have made toward the goal of paperless fingerprint processing, and (3) efforts being made to improve the timeliness of criminal fingerprint submissions.
Guides to Cooperating with Law Enforcement
Working with Law Enforcement: Asking the Right Questions
A Guide to Working with Law Enforcement for Medical and Emergency Personnel
Confidentiality and Coping with Law Enforcement Inquiries: Guidelines for the Library and its Staff
Increased visits to libraries by law enforcement agents, including FBI agents and officers of state, county, and municipal police departments, are raising considerable concern among the public and the library community. These visits are not only a result of the increased surveillance and investigation prompted by the events of September 11, 2001 and the subsequent passage of the USA Patriot Act, but also as a result of law enforcement officers investigating computer crimes, including email threats and possible violations of the laws addressing online obscenity and child pornography. These guidelines, developed to assist libraries and library staff in dealing with law enforcement inquiries, rely upon the ALA’s Policy on the Confidentiality of Library Records, its Policy Concerning Confidentiality of Personally Identifiable Information, and the Code of Ethics.
Assistance To Civilian Law Enforcement Agencies
United States Air Force guidance and procedures concerning support for Federal, state, and local civilian law enforcement agencies (LEA), specifying limitations and restrictions on using Air Force members and resources in the active and reserve forces, military and civilian, and the Air National Guard units or members when federalized.
Military Law Enforcement and Military Police
FM 19-10
Military Police Law and Order Operations
FM 3-19.1
Military Police Operations
FM 3-19.13
Law Enforcement Investigations
FM 3-19.15
Civil Disturbance Operations
FM 19-25
Military Police Traffic Operations
FM 3-19.30
Physical Security
FM 3-19.40
Military Police Internment/Resettlement Operations
FM 3-19.4
Military Police Leaders’ Handbook
Law Enforcement and Medical Records
HIPAA and Law Enforcement
New federal health information privacy regulations under the Health Insurance Portability and Accountability Act (“HIPAA”) change the way that hospitals are permitted to release and communicate patient information to law enforcement officers. This memorandum discusses how hospitals and law enforcement officers can interact in a way that does not violate these new federal regulations. It also discusses state laws that affect hospital law enforcement interaction.
HIPAA: Guidelines for Law Enforcement
The development and implementation of the Health Insurance Portability and Accountability Act (HIPAA) has been occurring over the last several years, but only recently went into effect as of April 14, 2003. The long-term ramifications of this federal legislation are unclear; however, immediate effects are already being felt by local and state law enforcement agencies. Health care entities are being educated on the regulations, with emphasis on the civil and criminal penalties attached to wrongful disclosures. While both federal and state regulations are clear with regards to investigative efforts, reluctance to disclose ANY Protected Health Information (PHI) is the result. Our purpose in developing guidelines for law enforcement is to 1) present the HIPAA regulations that directly and indirectly apply to law enforcement efforts in a death investigation, 2) discuss the implications for death investigations and obtaining information, and 3) provide recommendations for applying both state and HIPAA mandates appropriately to death investigations.
Miscellaneous Library Materials Relating to Law Enforcement
LAPD SWAT Team History
A history of the LAPD SWAT Team, including details of operations and equipment.
Police and SWAT
A history of SWAT Teams, focusing on the changing requirements and tactics of the last thirty years and the potential need for regulation.
A Resource Guide To Law Enforcement, Corrections, And Forensic Technologies
The wave of technological advancement that has changed the lives of almost every individual, business, and institution in the Nation has also changed the world of criminal justice - from how we fight crime to how we manage law enforcement resources to the types of crimes we face. New technologies can help criminal justice agencies prevent crime, apprehend criminals, manage offender populations, and protect the public against the threat of terrorism. This Guide seeks to provide helpful information to law enforcement, corrections, and forensic science professionals as they evaluate, acquire, and use equipment and technology.
Public versus Private Law Enforcement: Evidence from Bail Jumping
After being arrested and booked, most felony defendants are released to await trial. On the day of the trial, a substantial percentage fail to appear. If the failure to appear is not quickly explained, warrants are issued and two quite different systems of pursuit and rearrest are put into action. Public police have the primary responsibility for pursuing and rearresting defendants who were released on their own recognizance or on cash or government bail. Defendants who made bail by borrowing from a bond dealer, however, must worry about an entirely different pursuer. When a defendant who has borrowed money skips trial, the bond dealer forfeits the bond unless the fugitive is soon returned. As a result, bond dealers have an incentive to monitor their charges and ensure that they do not skip. When a defendant does skip, bond dealers hire bail enforcement agents, more colloquially known as bounty hunters, to pursue and return the defendants to custody. We compare the effectiveness of these two different systems by examining failure to appear rates, fugitive rates and capture rates of felony defendants who fall under the respective systems. We apply propensity score and matching techniques.
Federal Law Enforcement: Information on Use of Arrest Statistics
The 21st Century Department of Justice Appropriations Authorization Act (P.L. 107-273) requires GAO to report on how investigation and arrest statistics are reported and used by federal law enforcement agencies. This report provides information on (1) the guidance and procedures followed by federal law enforcement agencies regarding counting investigations and arrests, (2) how investigation and arrest statistics are used, and (3) whether multiple agencies are counting and reporting the same investigations and arrests. GAO selected six agencies for review: the Drug Enforcement Administration (DEA), the Federal Bureau of Investigation (FBI), the former Immigration and Naturalization Service (INS), the U.S. Marshals Service, the former U.S. Customs Service, and the U.S. Postal Inspection Service (USPIS).